Secure Your Hiring Process Against Candidate Fraud
.png)
Candidate Fraud by the Numbers

Source: Gartner
.png)
Source: GetReal-sponsored Research
.png)
Source: Gartner & HR Executive
Why Fake Candidates Are an Enterprise Security Threat
CHRO and talent acquisition leaders own what’s become an enterprise’s most exposed entry point – the hiring process. Nearly every Fortune 500 company has hired at least one North Korean operative. The adversary doesn’t need malware; they use AI-generated resumes, synthetic identities, and fabricated work histories.
In one case, a cybersecurity firm hired a DPRK IT worker who passed multiple video interviews and background checks, only to be caught after onboarding when they attempted to install malware on company equipment. And nation-state actors are only one part of the problem: financially motivated fraudsters, criminal networks, proxy interviewees, and overemployed workers all exploit the same weaknesses in hiring processes that weren’t designed to detect them.
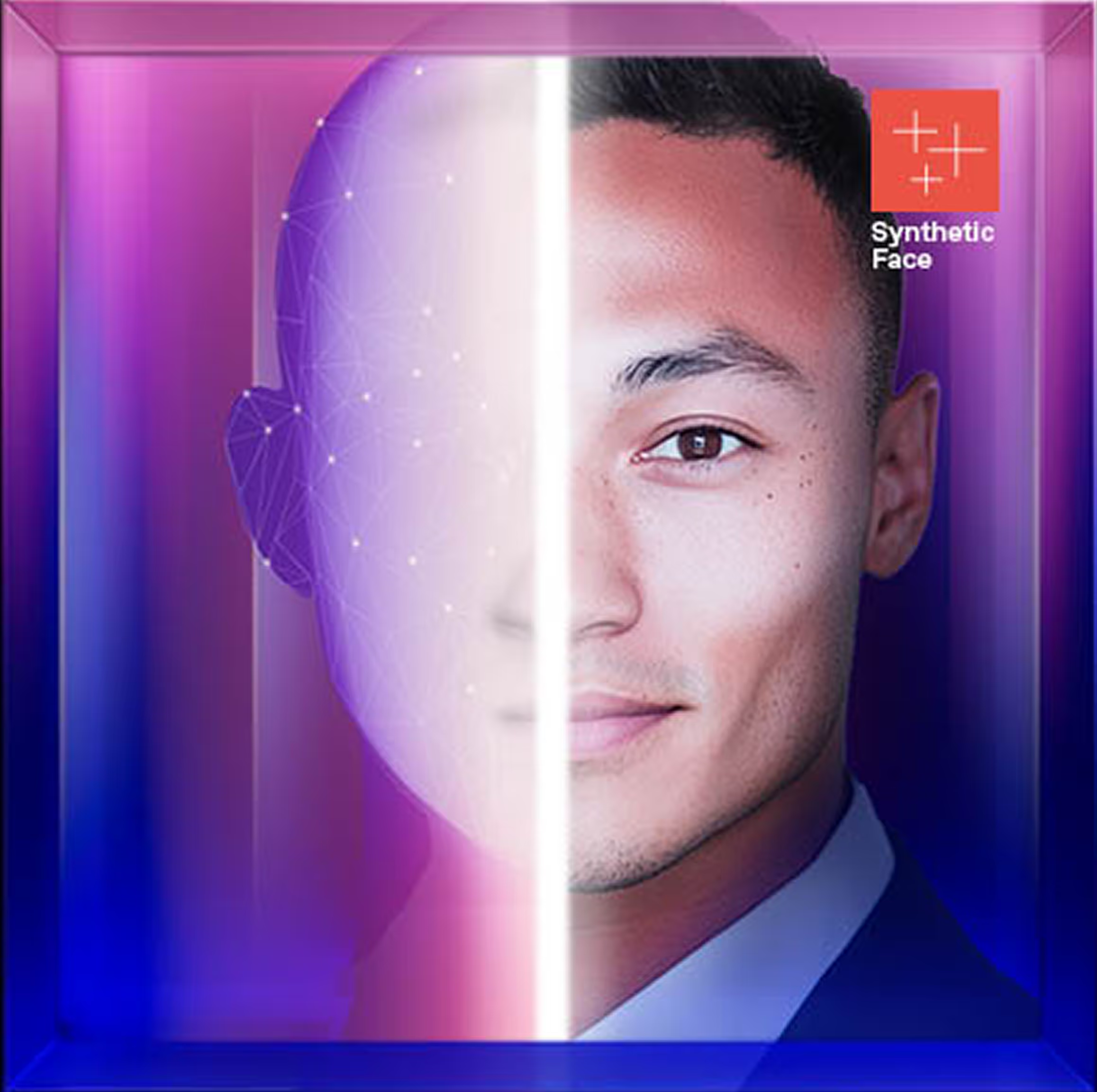
Why Background Checks and KYC Can’t Stop Candidate Fraud
Remote interviews don’t qualify as identity verification when there’s no true validation of the human on the other end. Background checks run against a stolen or rented identity will come back clean regardless of who submitted it. KYC bypass kits sold on the dark web package identity documents with liveness check videos and photos, or provide templates imposters can insert their face into to defeat identity verification solutions.
And point-in-time verification only confirms identity for a single moment or session, with nothing to flag inconsistencies in who shows up in subsequent interactions.
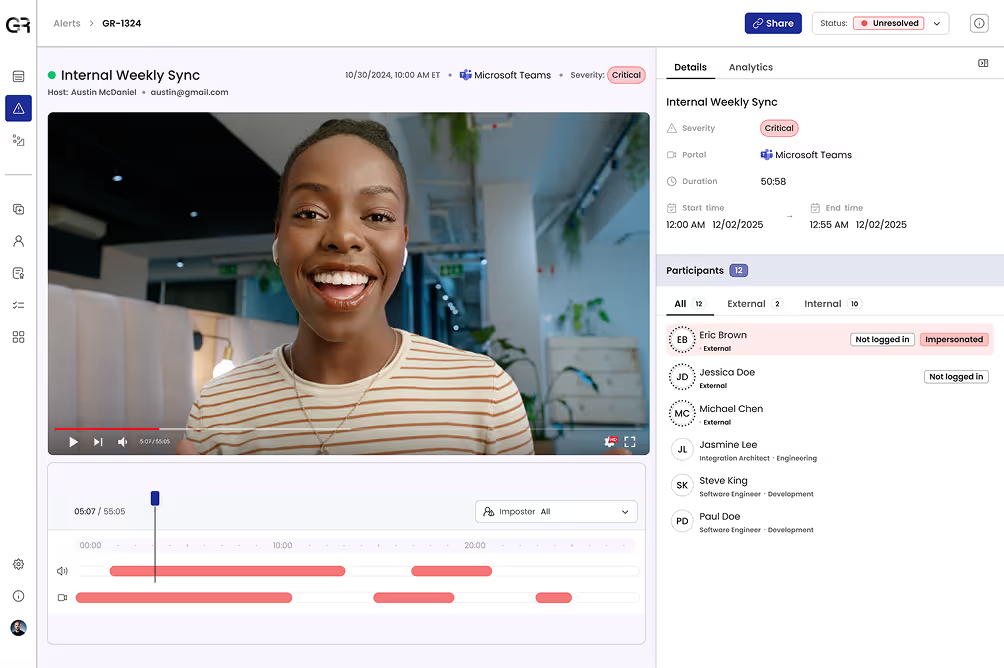
Rigorous Deepfake Detection
Automatically flag AI voice changers, face swapping, and other deepfake tools used by fraudulent candidates during screening and interviews. Detection grounded in forensic science minimizes false positives and produces defensible forensic evidence that stands up to legal and regulatory scrutiny.
Continuous Identity Verification
Verify candidate identity and confirm consistency across every interaction from screening through interviews, onboarding, and beyond. Verification happens automatically during digital interactions, requiring no effort from recruiters, hiring managers, or candidates.
Adaptive, Automated Response
Screenings and interviews are protected automatically without staff needing to intervene. When a violation is detected, adaptive policy enforcement based on your governance framework removes imposters from the pipeline without requiring staff to respond in the moment.
Global Threat Intelligence
Identify and block known bad candidates and repeat offenders – including North Korea-linked IT workers – before they move through the hiring process. Curated intelligence spanning your environment and the wider threat landscape correlates patterns to stop imposters in real time.
Can You Spot a Deepfake Candidate Before They're Hired?
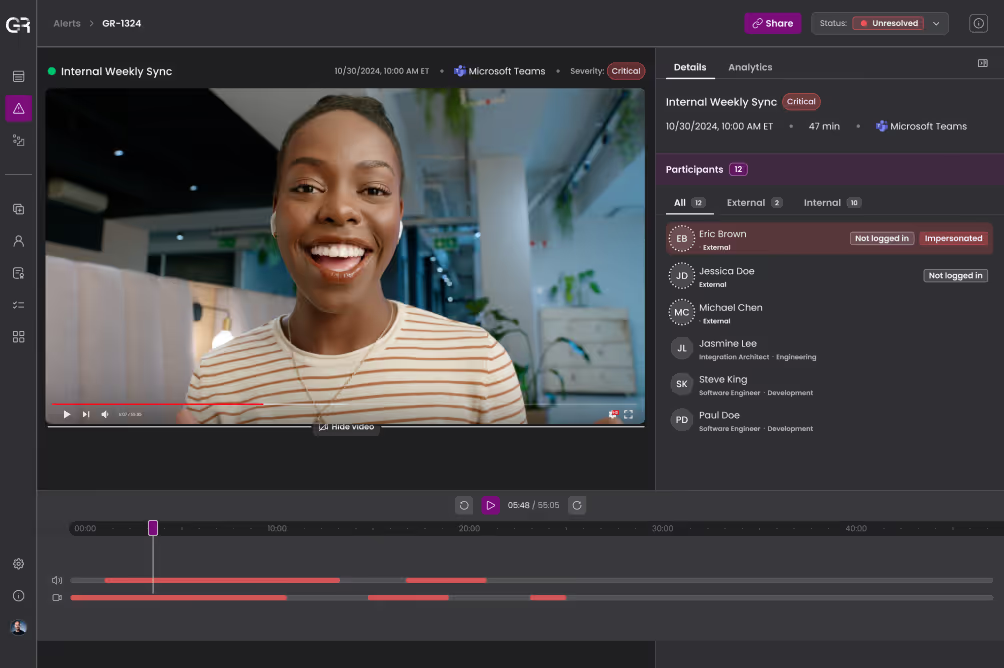
Outcomes for HR, Talent Acquisition, Recruiting, and Security Teams
- Stop imposter hiring and insider threats before they’re granted access to corporate systems, credentials, and sensitive data
- Reduce wasted recruiting, interviewing, onboarding, and rehiring costs by identifying and removing deceptive candidates early in the hiring lifecycle
- Demonstrate due diligence to leadership and compliance teams and avoid regulatory exposure resulting from the hiring of individuals from sanctioned nations

Understand Deepfake & AI-Powered Identity Threats by Role
See Your Hiring Process Through an Imposter’s Eyes