Workforce Integrity for the Extended Enterprise

Workforce Identity Risk by the Numbers

Source: Gartner
.png)
Source: GetReal-sponsored Research
.png)
Source: Gartner & HR Executive
Why Your Extended Workforce Is an Identity Blind Spot
Workforce relationships begin with an assumption: the person verified in initial interviews through onboarding is still the same person showing up each day. Today’s workforce includes not only employees, but also SOW work, contractors, freelancers, BPO partners, and contingent workers.
All of these groups are granted varying degrees of trust and insider access without consistent screening processes across the board. AI-created identities and deepfakes that fool recruiters also work in contractor check-in calls. Imposters may install ransomware, steal IP, or lead toregulatory exposure for engaging with sanctioned countries, entities, or persons. Without continuous verification, assurance of the actual human behind a previously verified identity degrades over time.
Why Siloed Controls Can’t Assure Workforce Identity
In most organizations, no single function owns workforce integrity, and the controls to protect it are siloed. HR typically owns the direct employee hiring and onboarding process, whereas procurement usually manages outsourcing. Checks exist in isolation without any connected system or persistent thread of identity assurance across teams, vendors, and time.
Traditional security controls authenticate devices and credentials, not the human behind them or whether the human in this interaction is the same one as in the last. Deepfakes, stolen credentials, and other deceptive methods exploit those gaps.
For staffing firms, MSPs, RPOs, and BPOs, the platform provides assurance across hand-offs to their clients that workers are continuously verified, not just screened at intake.
Rigorous Deepfake Detection
Identity can only be verified in remote interactions if associated image, audio, and video files and streams are authentic. Automatically detect deepfake tools with explainable, defensible evidence for automated response, audit, and legal review.
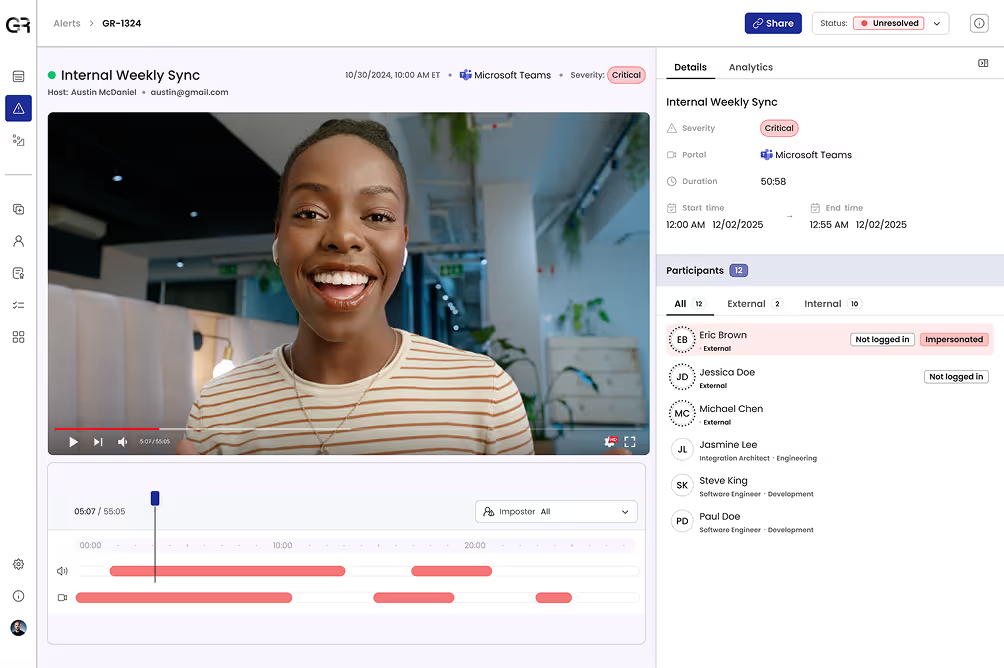
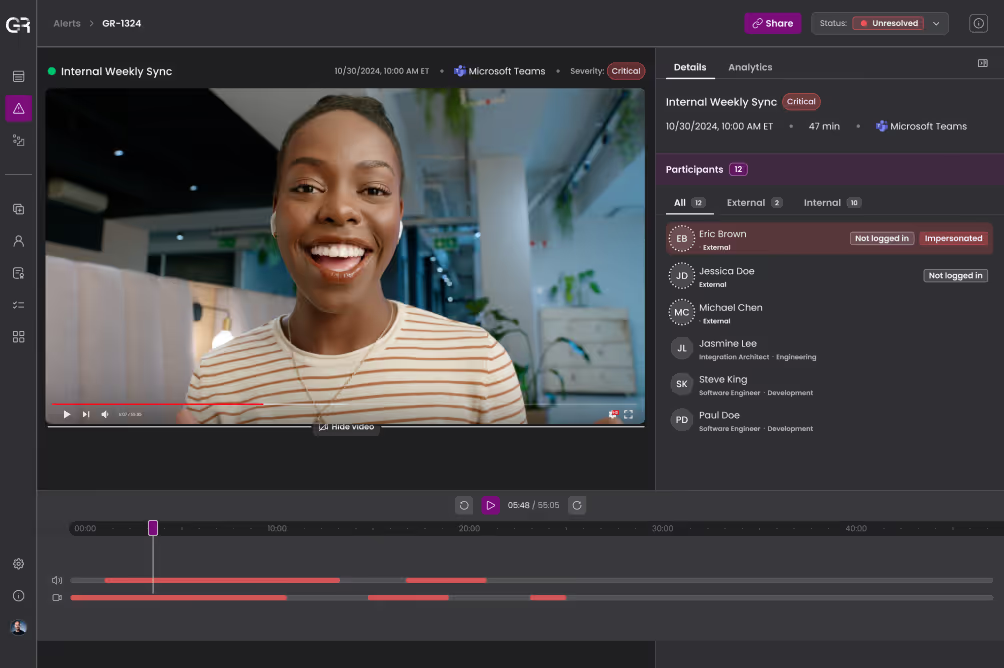
Continuous Identity Verification
Verify identity at onboarding and continuously maintain assurance across subsequent digital interactions. Automatically confirm consistency of identity attributes across calls and meetings to flag violations whether deepfakes are involved or not.
Adaptive, Automated Response
If a violation is detected, trigger responses automatically according to corporate policies without requiring anyone to intervene. Limit exposure, prevent disruption of the legitimate workforce, and ensure every worker type is treated consistently and fairly.
Global Threat Intelligence
Identify and block known imposters before they gain a foothold in your workforce. Information about these individuals including behavior patterns, location, and their actual faces and voices means repeat offenders can’t reappear under a different identity.
Outcomes for Security, HR, and Procurement Teams
- A workforce you can trust is who they claim to be across every worker type, every contractor relationship, and every digital interaction, not just at onboarding
- Automatic, consistent response to violations that prevents disruption of legitimate workers and provides defensible evidence when action is required
- Evidence for auditors and regulators substantiating that workforce identity is continuously verified, not assumed
- A verifiable record of identity assurance that staffing firms, RPOs, and BPOs can offer customers as a mark of trust and differentiation

Understand Deepfake & AI-Powered Identity Threats by Role
See Workforce Integrity in Action