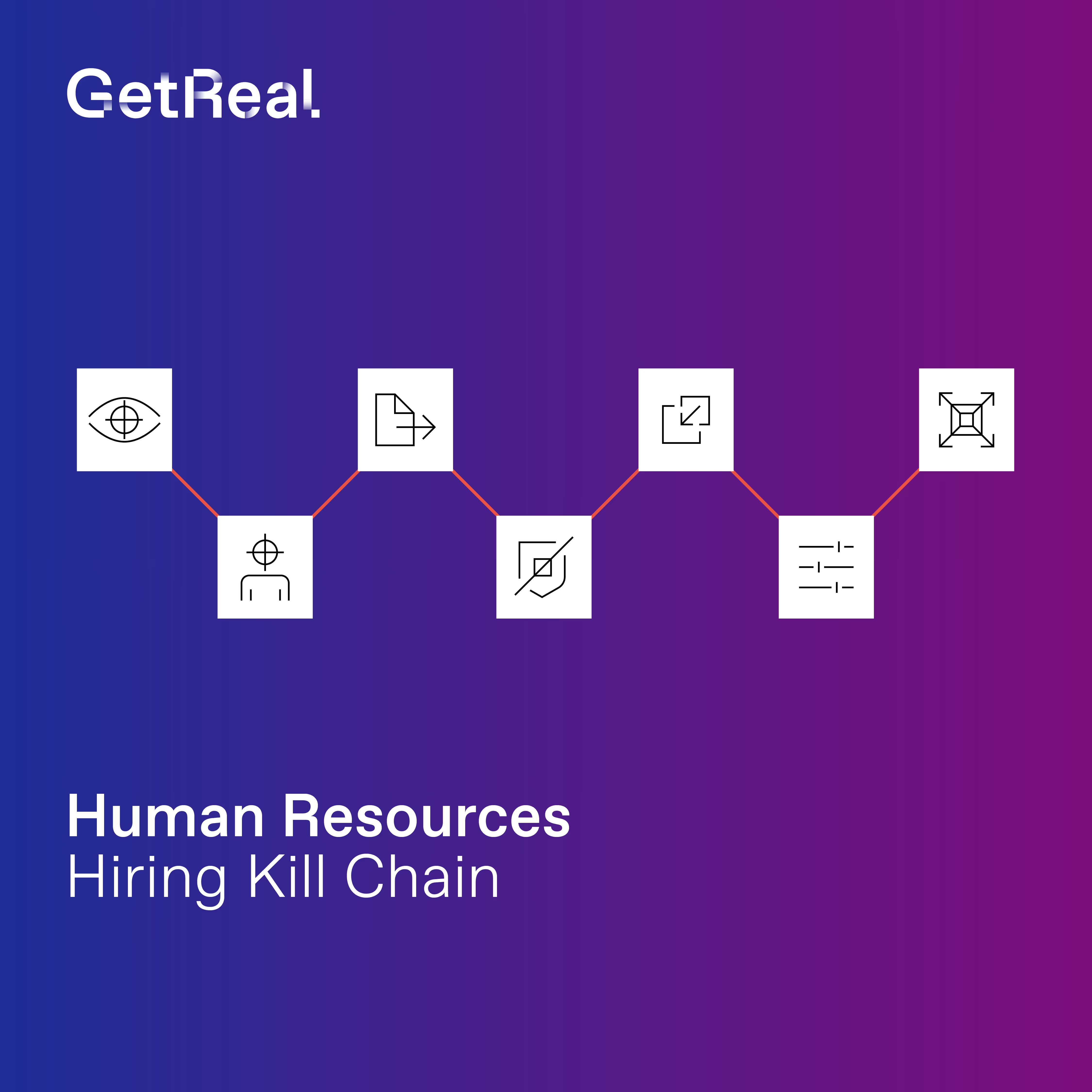
Deepfakes: The Trust Layer Built for Remote Work Is Being Exploited
These attacks don’t target your infrastructure — they exploit the trust assumptions embedded in how your organization uses it.

Deepfake Attacks on IT Infrastructure Are Accelerating
Source: Industry Report
.avif)
Source: Analyst Projection
Source: Industry Analysis
What CIOs Need to Know
The collaboration infrastructure you built for remote work has created a new attack surface: synthetic identity in live interactions.
When attackers can convincingly replicate identity during live interactions, they bypass technical controls and manipulate human workflows to gain access, authorize changes, and disrupt operations.
You own service delivery, operational stability, and technology enablement. When deepfakes compromise help desk processes or remote access workflows, the business disruption falls under IT operations.
What Prepared IT Organizations Are Doing
- Implement out-of-band verification for high-risk IT requests like password resets and MFA changes
- Deploy real-time detection tools for synthetic voice and video during live interactions
- Embed stronger identity verification into IT service management workflows
- Establish clear incident response playbooks with defined cross-functional roles
- Monitor evolving deepfake attack techniques targeting IT operations
Treat deepfake risk as a technology enablement and operational resilience issue. Consider deepfake preparedness a prerequisite for sustaining digital transformation.

Learn more by downloading our detailed guide here