Protect People Against Executive Impersonation

Executive Impersonation by the Numbers

Source: Indeed Flex
.png)
Source: The Guardian
.png)
Source: Wall Street Journal
Why Executive Impersonation Is the Next Evolution of BEC
When a finance manager receives an urgent call from the CFO asking for a wire transfer before a deal closes, they listen. They trust what they see and hear. Attackers know it and exploit that trust to target employees across finance, HR, legal, IT, and operations. CEO fraud and next-generation business email compromise attacks succeed because traditional security controls don’t extend into the human layer of digital interactions.
Cloned executive voices and deepfaked video can short-circuit employee reasoning, and the output of these tools only continues to improve in fidelity. Research finds humans recognize a voice as AI-generated only slightly better than chance.
Why Email Security and Training Can’t Stop Voice and Video Attacks
Email security gateways don’t inspect voice and video calls where BEC 2.0 attacks now live. Voice and video-based impersonation falls outside the scope of authentication, which validates credentials rather than whether the entity on the other side of a digital interaction is the human they claim to be. As deepfake quality and text-to-speech tools continue to improve, security awareness training-based detection tips become outdated faster than training can be refreshed, resulting in a false sense of security.
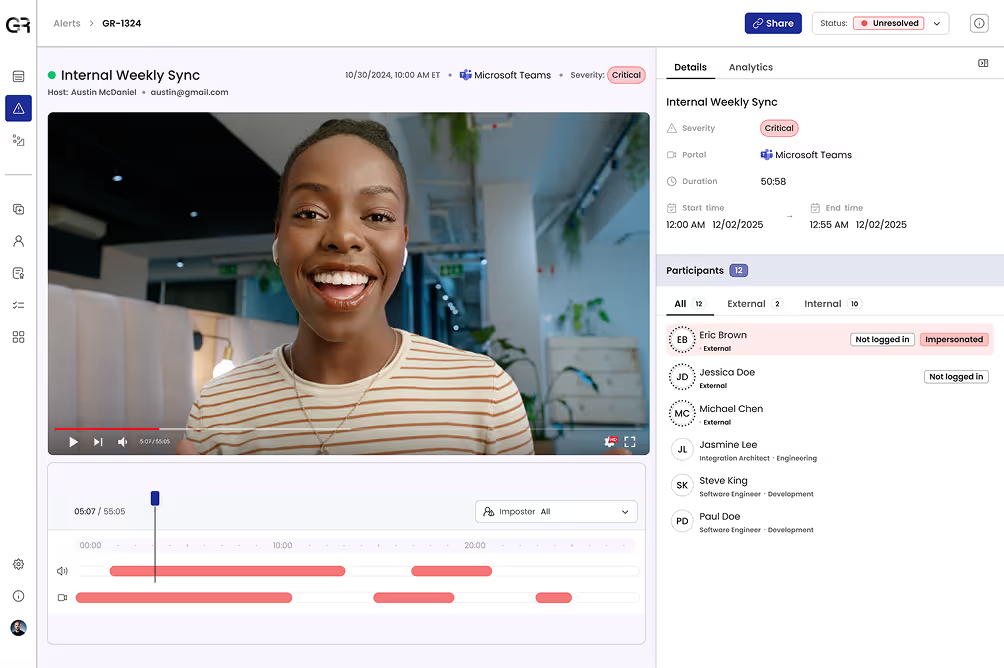
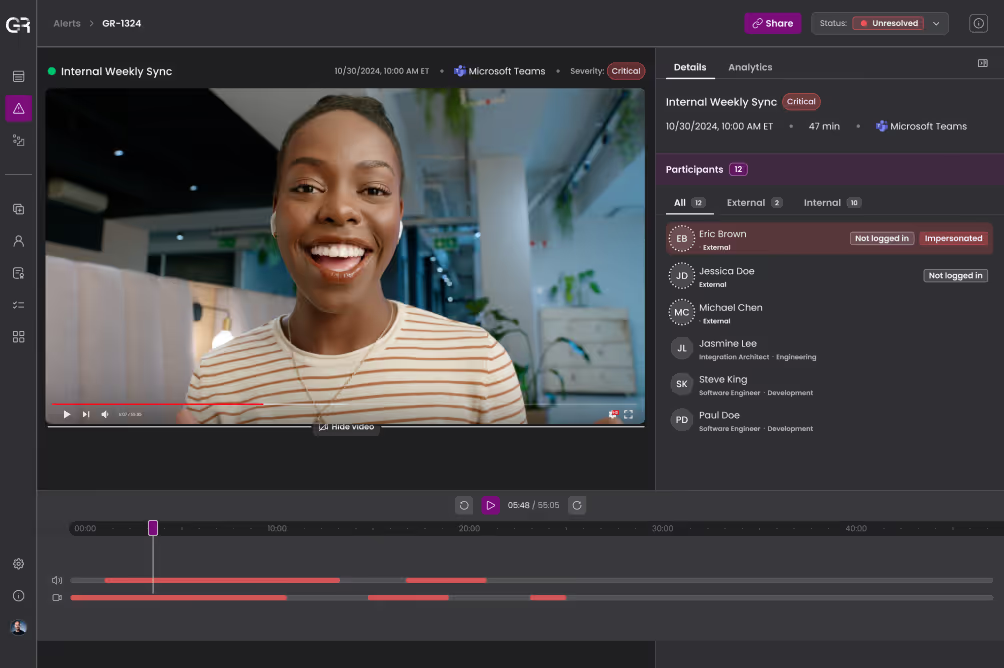
Rigorous Deepfake Detection
Detect AI-cloned voices, face-swapped video, and synthetic avatars used to impersonate executives in live calls and recorded communications. Forensic evidence of manipulation minimizes false positives and holds up to scrutiny.
Continuous Identity Verification
Continuously verify executive identity across digital interactions, building an understanding of authentic identity that is more reliable than any impersonator can replicate.
Adaptive, Automated Response
Automatically enforce policy on detections to stop impersonations before they cause damage. Alert security teams and block high-risk actions through seamless integration with existing enterprise workflows.
Global Threat Intelligence
Identify threat actor TTPs and attack patterns in real-time voice and video interactions. Correlate signals across the enterprise to surface coordinated, multi-channel impersonation campaigns.
Outcomes for C-Suite, Finance, Security, and Operations Teams
- Stop fraudulent wire transfers and other unauthorized transactions triggered by executive impersonation before employees act on them
- Remove the burden of real-time deepfake detection from employees to stop attacks that humans can’t reliably spot
- Generate defensible, forensic evidence of impersonation attempts to support incident response and investigations

Understand Deepfake & AI-Powered Identity Threats by Role
See Your Organization Through an Impersonator’s Eyes